UT Austin ISO
Information Security Service Offerings
Artisanally-crafted infosec goodness. The results from these services are verified, so you won't have to waste time with false positives or distractions
Getting started is easy and done in the same day.
Our services are meant to be extremely low-friction. No setup required, just subscribe and we'll handle the rest.
Our services are battle-tested across global deployments and will add an excellent layer of added protection to your Information Security Program.
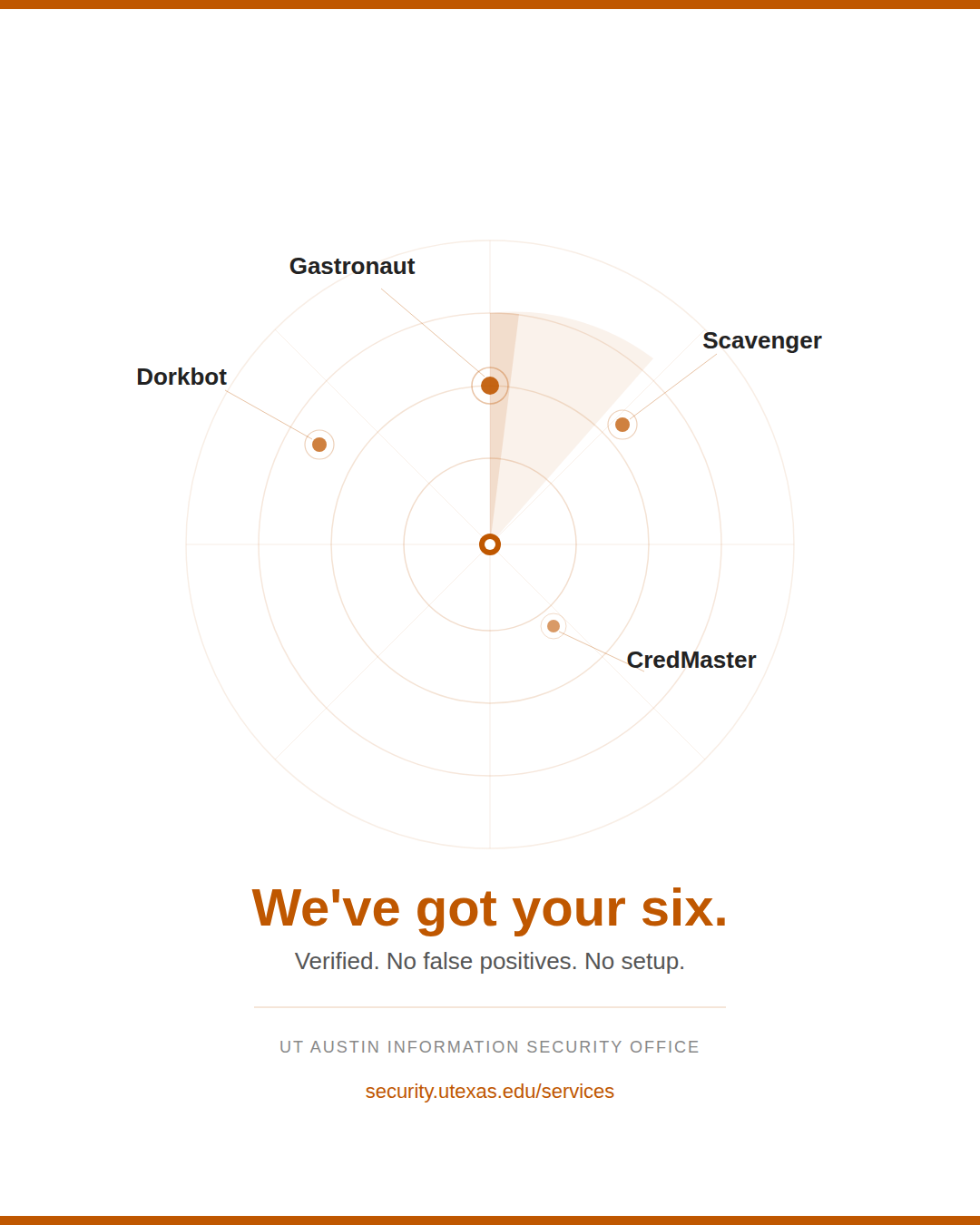
Our Capabilities
Information Security Services
Comprehensive assessment services built to be accurate and actionable.
Free
Dorkbot — Web Vulnerability Scanning
- Currently serves 5,250+ entities across 205 countries
- Uses cached crawl data to detect common web vulnerabilities
- No active crawling, low friction, zero impact on live services
- Verified results only, no false positives, no noise

Managed Service = $1500 PER YEAR
Gastronaut — Advanced Web Vulnerability Scanning
- Crawls sites to uncover hard-to-find vulnerabilities
- Leverages an expanded, modern rule set built for real-world application environments
- Delivers verified, actionable findings through monthly reporting

Managed Service = $1500 PER YEAR
CredMaster — Dark Web Monitoring
- Scans dark web for stolen credentials tied to your domain(s)
- Verifies if exposed credentials are still active before alerting
- Provides immediate alerts and reports upon confirmed exposure

Managed Service = $1500 PER YEAR
Scavenger — Attack Service Intelligence Scanning
- Identifies & alerts on vulnerable external facing assets (weekly)
- Provides a comprehensive view of exposure to cyber threats
- Enables proactive risk mitigation and security hardening

Assessment = CHARGED PER HOUR
Application Security Assessments
Web or supplicant applications are assessed by our team for security vulnerabilities and compliance gaps. Provides a comprehensive view of exposure to cyber threats

Assessment = CHARGED PER HOUR
Controlled Penetration Testing
Identified vulnerabilities are verified and exploited in a controlled environment to determine the extent of potential weaknesses, attack vectors, and pivot points.
End-to-end security services, built for your environment.
From uncovering exposed attack surfaces to monitoring the dark web for stolen credentials — our suite of services covers the threat landscape and your institution's unique risks.
Get Started
Interested in our Information Security Services?
Tell us about your organization, the services you're interested in, and we'll get right back to you.